Software patches are a foundational pillar of cybersecurity, delivering targeted fixes that close vulnerabilities and harden defenses across networks, endpoints, and cloud environments. A well-structured patch management process coordinates discovery, testing, approval, deployment, and verification to ensure these fixes reach production safely. Many teams compare software updates vs patches to decide priorities, recognizing that patches focus on closing security gaps while updates may add features. Security patches are critical for reducing exposure, supporting vulnerability remediation, and accelerating incident response across the stack. Adopting patch deployment best practices—such as phased rollouts, robust testing, and clear rollback plans—helps minimize risk while preserving business continuity.
Beyond the basics, teams talk about patching and remediation in ways that emphasize preparation, risk reduction, and governance. Think of these efforts as security hardening, where fixes—sometimes called vulnerability remediation or defensive updates—tighten configurations and reduce exploitable paths. A well-managed lifecycle combines asset inventory, change control, testing in isolated environments, and a measured rollout to production, mirroring best practices in update governance. From a performance and compliance standpoint, this holistic approach aligns with repair-oriented thinking, continuous monitoring, and documented rollback strategies. By framing patches as part of a broader maintenance discipline rather than isolated events, teams can sustain secure operations without sacrificing agility.
Understanding software patches vs updates: distinguishing patching from feature enhancements
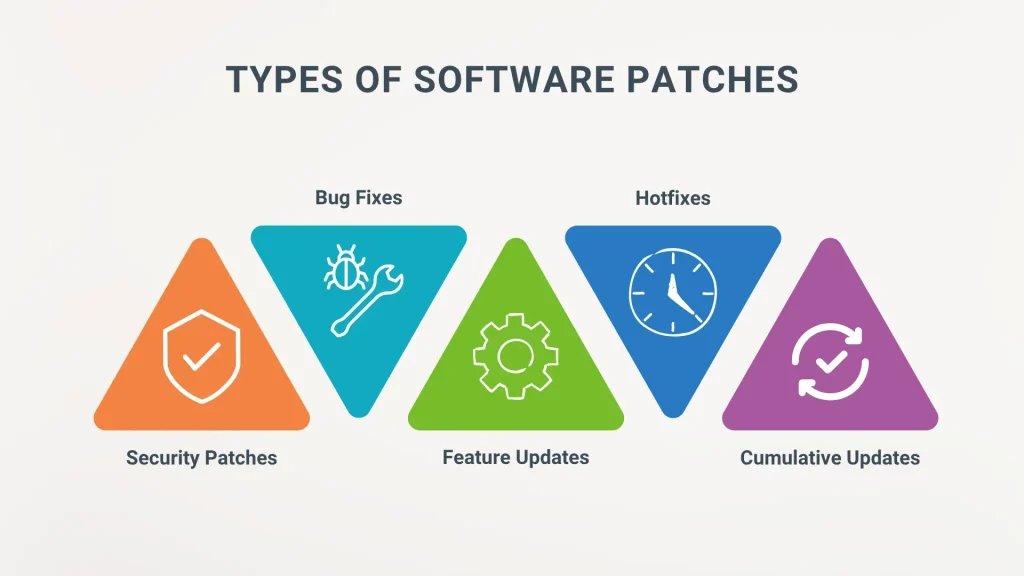
Software patches are targeted fixes released by vendors to address specific issues, often security vulnerabilities, bugs, or reliability flaws. They repair a flaw without dramatically changing surrounding functionality, which is different from broad feature updates. This helps clarify the concept of software patches and explains why teams should treat them with priority in risk management.
Understanding software updates vs patches helps teams triage what needs immediate attention. In security-focused environments, patches take precedence, while software updates vs patches becomes a key decision point for prioritization. A clear policy that differentiates these actions supports a consistent approach to patch management and risk-based scheduling.
The strategic role of security patches in vulnerability remediation
Security patches are the primary tool in vulnerability remediation. They address known weaknesses before attackers can exploit them, reducing exposure across critical systems. Organizations should monitor CVEs and vendor advisories, weaving security patches into a predictable patch management cadence.
Delaying security patches increases risk, especially for internet-facing services and databases. A structured approach — inventory, risk scoring, testing, deployment, and verification — ensures vulnerability remediation happens in a controlled, auditable manner.
How to design a robust patch management program
A robust patch management program begins with clear policy, a complete asset inventory, and a centralized view of patch status across operating systems, applications, and firmware. This visibility supports consistent prioritization and faster remediation.
Automation is essential to scale patch management, enabling discovery, prioritization, deployment, and reporting, while human oversight ensures risk-based decisions remain central. A mature program couples automation with governance to sustain performance over time.
Patch deployment best practices: from testing to phased rollouts
Patch deployment best practices emphasize a phased deployment model to minimize disruption. Start with a small group of systems, use canary testing or blue-green strategies, and schedule maintenance windows to reduce user impact.
Automate where feasible and ensure robust rollback plans. After deployment, conduct verification to confirm patch success and monitor for any post-deployment issues, maintaining clear traceability throughout the process.
Testing, validation, and controlled environments for effective patching
Testing and validation should occur in a controlled environment that mirrors production, validating compatibility with configurations, integrations, and security controls. This helps prevent regressions and ensures patches won’t disrupt critical workflows.
Establish acceptance criteria, run functional and security tests, and document outcomes to prevent regressions and support audits. A disciplined testing regime is a cornerstone of reliable vulnerability remediation and successful patch deployment.
Patching across diverse environments and ensuring compliance
Patching across diverse environments requires tailored approaches for Windows, Linux, applications, middleware, firmware, and cloud services. A unified patch management strategy should accommodate these differences while maintaining visibility and control.
Documentation, compliance reporting, and governance ensure that security patches and vulnerability remediation align with regulatory requirements and internal policies. Continuous improvement of processes helps sustain resilience across all environment types.
Frequently Asked Questions
What are software patches, and how do they relate to software updates vs patches?
Software patches are targeted fixes that address specific vulnerabilities and bugs, focusing on remediation without broad changes to functionality. Software updates vs patches: updates may add features or improvements, while patches primarily fix known problems and close security gaps. Understanding this distinction is essential for vulnerability remediation and for prioritizing what to apply first.
Why are security patches essential for vulnerability remediation, and how does patch management support this?
Security patches are the primary line of defense against exploited vulnerabilities. Effective patch management orchestrates identification, testing, approval, deployment, and verification of these patches, ensuring timely vulnerability remediation and minimizing exposure.
What is patch management, and why is it a core part of patch deployment best practices?
Patch management is the ongoing process of discovering, prioritizing, testing, deploying, and tracking patches across systems. It underpins patch deployment best practices by providing a repeatable, auditable routine that reduces risk, ensures compliance, and minimizes disruption.
What are patch deployment best practices to minimize risk when applying patches across environments?
Key practices include separating security patches from feature updates, using phased deployment, testing patches in representative environments, automating inventory and deployment where possible, establishing rollback plans, verifying post-deployment success, and documenting outcomes for auditability.
How should patching be approached across different environments under a unified patch management strategy?
Tackle patching across Windows, Linux, applications, firmware, and cloud services by maintaining a centralized patch management strategy. Tailor testing and deployment to each environment—Windows Patch Tuesday cadence, Linux security advisories, and cloud-provider patching—to ensure consistency and minimize risk.
How do you decide when to apply patches versus waiting for updates in security-sensitive settings, balancing vulnerability remediation and business needs?
Prioritize security patches with known critical vulnerabilities to accelerate remediation, even if it delays broader software updates. Use risk-based assessment, change control, and maintenance windows to balance security with availability, ensuring continuous vulnerability remediation without compromising business operations.
| Topic | Key Points |
|---|---|
| What are patches vs updates? | Patches are targeted fixes addressing specific issues (security vulnerabilities, bugs, performance problems). They repair a flaw with minimal changes to surrounding functionality. Updates can add features, enhancements, or broad changes and may include security fixes, but they are not as narrowly focused as patches. |
| Why patches matter | Security patches are critical; proactive patching reduces risk as threats exploit unpatched software. They require a proactive patching schedule, a complete inventory, and a testing process before broad deployment. |
| How patches are released and who should patch | Vendors release patches in response to vulnerabilities or defects; large organizations may track CVEs. The patch management cycle typically includes discovery, assessment, testing, approval, deployment, and verification. |
| Understanding patch management | An ongoing discipline covering OS, applications, middleware, firmware, and embedded devices; relies on centralized policy and automation. Key components include: asset/inventory management, risk-based prioritization, testing/staging, deployment strategies, rollback/recovery, and compliance/reporting. |
| Patch deployment best practices | 1) Separate patching from feature updates; 2) Phased deployment; 3) Test in a representative environment; 4) Automate where feasible; 5) Establish rollback plans; 6) Verify post-deployment; 7) Document and audit. |
| Patch management across environments | Windows: Patch Tuesday and prompt testing; Linux: security advisories and repositories; Applications/middleware: vendor patches; Firmware/IoT: downtime or staged updates; Cloud/SaaS: patches managed by the provider with attention to compliance, data residency, and access controls. |
| Software updates vs patches: a practical perspective | Context matters: in security-focused environments, patches for critical vulnerabilities take precedence; regulated industries may require change control; agile teams may enable continuous patching with strong monitoring. |
| Addressing common myths | Myth: Patches always cause downtime. Reality: With careful testing and phased deployment, downtime can be avoided. Myth: Patches are only for software. Reality: Firmware patches are essential too. Myth: All patches are created equal. Reality: Critical patches require prioritization. Myth: You can patch once and forget it. Reality: Patch management is ongoing with new vulnerabilities. |
| A simple framework you can apply today | Inventory all systems; classify vulnerabilities by risk; set maintenance windows and patch calendar; test in controlled environments; roll out in phases; verify success; document outcomes and adjust processes. |
Summary
Software patches play a foundational role in cybersecurity and operational reliability. They differ from broad updates by targeting specific flaws, vulnerabilities, or bugs rather than wide-ranging feature changes. A mature patch management program relies on policy, comprehensive asset inventory, risk-based prioritization, thorough testing, and phased deployment to minimize disruption. By applying best practices—separating patching from feature updates, automating where possible, validating patches in representative environments, and maintaining rollback plans—organizations can reduce exposure to threats while preserving daily productivity. In short, effective software patches enable safer, more resilient IT environments and support ongoing business continuity.